Scammers constantly refine their digital traps to exploit the speed of modern life. You will encounter schemes that look like legitimate opportunities but lead to financial ruin. These predators rely on psychological pressure to force quick decisions before your logic kicks in. The internet is a playground for those who know how to manipulate a sense of urgency.
Why referring to "rotten chilli dogs"? Because simply, those scammers make you feel like you've eaten something really bad that stay in your stomach making you ill for a few days, at least. No matter how you try to be positive, telling yourself you've learned a lesson, the damage can be so huge that could traumatise you for years. Make you feel rotten, for sure.
You must view every unsolicited message with a high degree of skepticism to protect your assets. Modern traps are far more sophisticated than the clunky emails of previous decades. Criminals use social engineering to bypass your security and gain direct access to your bank accounts. Your awareness of these tactics acts as a shield against the most clever digital thieves. You should treat every notification as a potential threat until you verify its origin. Each section breaks down the logic behind the trap to keep you safe. Preparation is the only defense in a landscape filled with hidden risks.
1. Phishing Scams
Low-quality lures often hide behind familiar brand names to steal your login credentials. You see a message that claims your account will be deleted within the hour. This specific tactic relies on the fear of losing access to your digital life. The link provided leads to a counterfeit page that looks identical to the real website. You enter your password and unwittingly hand over the keys to your personal data.
Digital thieves use these "rotten" lures because they only need a small percentage of people to fail. Most filters catch these messages, but a few always slip through the cracks. You should inspect the sender's email address for subtle misspellings or unusual domains. These minor errors are the first sign that the message is a fabrication. Professional companies will never ask for your password via an unencrypted email link.
Security measures like two-factor authentication will stop this attack in its tracks. You must enable these protections on every sensitive account you own. Even if a thief has your password, they still require the physical code from your device. This extra layer of defense makes your data a much harder target for criminals. You remain in control of your destiny when you prioritize technical safeguards over convenience.
- Check the URL bar for a padlock symbol and the correct domain name before you type. Fake sites often use letters from different alphabets that look similar to standard characters.
- Report the phishing attempt to the actual company to help them shut down the malicious site. Organizations have departments dedicated to tracking and neutralizing these digital threats.
- Delete the message immediately if it demands urgent action without prior notice. Legitimate service updates usually arrive with a clear history of communication and official documentation.
2. Remote Tech Support Extortion Scripts
Pop - up windows that claim your computer is infected are almost always a lie. You see a flashing red screen that tells you to call a toll - free number. This script is designed to induce panic and force you to surrender control of your machine. The person on the other end will pretend to run a scan of your files. They show you harmless system logs and claim they are signs of a massive virus.
Criminals want to install remote access software on your desktop to steal your banking information. You will pay hundreds of dollars for a "fix" that actually installs more malware. These individuals rely on your lack of technical knowledge to make their claims sound plausible. They often ask for payment in the form of gift cards or cryptocurrency to avoid detection. No legitimate software company will ever contact you through a browser pop - up to demand money.
Disconnecting your internet is the fastest way to stop an active remote session. You should run a scan with a reputable antivirus program that you already trust. Change all your passwords immediately if you allowed someone to access your computer. Notify your bank if you shared any financial details during the phone call. Your proactive response will limit the damage caused by these high - pressure tactics.
Close your browser using the task manager if a pop - up freezes your screen. This method bypasses the malicious script that prevents you from clicking the "X" button.
Search for the phone number online to see if other people have reported it as a scam. Public forums often list the exact scripts used by these offshore call centers.
Install an ad - blocking extension to prevent these malicious windows from appearing in the first place. Better browser security reduces the chances of you encountering these fraudulent alerts.

Job scams promise easy remote work but require upfront payments or personal info, leading to financial loss or identity theft. With remote work booming, these frauds spiked in 2025, with the IC3 reporting over 50,000 complaints and $200 million in losses. Scammers post fake listings on sites like Indeed or LinkedIn, often involving reshipping goods or fake checks.
In a 2025 case, a victim from Texas was "hired" for a data entry job but asked to buy equipment with a provided check that bounced, leaving her $3,000 in debt. Another example: Phony recruiters on WhatsApp offered high-paying product review gigs, requiring a "deposit" for access, scamming thousands globally.
Red Flags:
- Upfront fees for training, kits, or background checks.
- Overpayment scams where you refund "extra" from fake checks.
- Jobs promising high pay for minimal effort.
- Unsolicited offers via text or email.
- Requests for sensitive info like SSN early on.
Prevention Tips:
- Verify companies on the Better Business Bureau (BBB) or Glassdoor.
- Never pay to apply or work; legitimate employers cover costs.
- Search for the job description online to spot duplicates.
- Use official job boards and company websites.
- Enable two-factor authentication on job search accounts.
Report to the FTC, IC3, and the job platform. If checks are involved, contact your bank immediately. For identity theft, request free credit reports and place fraud alerts. Resources like the Department of Labor's CareerOneStop can help find legitimate opportunities.
3. Ghost Rental Listings and Deposit Theft
Fraudulent landlords post pictures of luxury apartments at prices that are too good to be true. You find a listing that seems like a perfect deal in a competitive market. The owner claims they are out of the country and cannot show the unit in person. They ask for a security deposit via a wire transfer to hold the property for you. You send the money and never hear from the person again because the apartment was never theirs.

Real Estate
Reverse image searches often reveal that the photos were stolen from a real estate website. You should always insist on a physical tour of the property before any money changes hands. Scammers use the high demand for housing to rush you into a bad financial decision. They tell you that five other people are interested and you must pay now. Your patience is a mandatory defense against this type of real estate fraud.
Public records will tell you who actually owns the building you are looking to rent. You should verify that the person you are talking to has the legal right to lease the space. Use a credit card or a secure payment platform that offers fraud protection for your deposit. Avoid any "landlord" who insists on cash or untraceable wire transfers. Legitimate businesses have no problem providing a paper trail for every transaction.
Verify the property owner's name through local government tax records or land registries. Matching the name on the lease to the official record prevents many common identity frauds.
Drive by the address to see if the property actually exists and matches the photos. Scammers sometimes use addresses of empty lots or buildings that are currently under construction.
Speak with the neighbors to see if the unit is actually available for rent. People living nearby often know the history of the building and its true management.
4. Synthetic Cryptocurrency Investment Platforms
Fake trading apps promise massive returns with zero risk to your initial capital. You see advertisements featuring celebrities who claim to have made millions in a short time. These platforms show you a dashboard with fake profits that grow every single day. The numbers on the screen are nothing more than a digital illusion designed to keep you investing. You will find that withdrawals are impossible once you try to take your money out.
Withdrawal requests usually trigger a demand for "taxes" or "release fees" that you must pay upfront. You send more money in hopes of getting your original investment back, but the cycle never ends. These scammers use the complexity of blockchain technology to hide their trail of theft. They count on your desire for quick wealth to override your natural caution. Your logic should tell you that a guaranteed return of ten percent per day is a mathematical impossibility.
Verified exchanges have strict regulatory requirements and a history of public accountability. You should research the company's registration with financial authorities before you deposit a single cent. Anonymous developers who operate solely through social media apps are a major red flag. Keep your assets in a private wallet where you control the private keys. Self - custody is the only way to ensure that your digital wealth remains your own.
Check the domain age of the investment website using a public WHOIS lookup. New websites that claim to have years of success are lying about their history.
Search for "platform name + scam" to find reviews from other burned investors. Crowdsourced information is a reliable way to spot a fraudulent exchange before you join.
Consult with a certified financial advisor before you move large sums of money into digital assets.Professional advice provides a grounded perspective on the risks associated with volatile markets.
5. Romantic Manipulation and Fabricated Crisis
Scammers build a fake relationship with you over several months to gain your trust. You meet someone on a dating app who seems to have the perfect life and personality. They eventually tell you about a sudden medical emergency or a legal problem that requires cash. This person will claim they cannot access their own funds due to a temporary glitch. You send the money because you feel a sense of obligation to help your new friend.
Photos used in these profiles are often stolen from models or minor influencers in other countries. You should ask for a video call to verify that the person matches their pictures. Most scammers will make excuses about broken cameras or poor internet connections to avoid a live call. They target people who are looking for a genuine connection and use that desire as a weapon. Your emotional health depends on your ability to set boundaries with people you have never met.
Refusal to send money usually results in the person becoming aggressive or guilt - tripping you. You should block the account the moment they ask for financial assistance for any reason. Real relationships are not built on anonymous wire transfers or gift card codes. Inform the dating platform about the suspicious behavior to protect other users from the same trap. Your safety is more mandatory than the potential for a digital romance.
Run a reverse image search on the profile pictures of anyone you meet online. Finding the same photo on multiple profiles with different names is a clear sign of fraud.
Keep your personal financial details private during the initial stages of any meeting. Sharing your income or bank name makes you a target for more sophisticated social engineering.
Tell a trusted friend about the person and listen to their objective opinion. Outside perspectives often spot the inconsistencies that you might miss due to your feelings.
6. The Overpayment Refund Reversal
Buyers will send you a check for more than the agreed price of an item you are selling. You see that the amount is much higher than the actual cost of the product. The buyer tells you it was an accident and asks you to wire the difference back to them. You see the funds in your account and comply with the request to be a good person. The original check eventually bounces, and your bank deducts the full amount from your balance.
Banks often make funds available before a check has actually cleared the originating institution. You are responsible for the money if the check turns out to be a forgery. This scheme exploits the time delay in the global banking system to steal your hard - earned cash. Scammers prefer this method because it makes them look like the victim of a simple mistake. Your bank will not cover the loss because you authorized the outgoing wire transfer.
Waiting for a full ten days is the only way to be sure a check is legitimate. You should refuse any payment that exceeds the price of the item you are selling. Honest buyers will have no problem sending the correct amount through a verified payment service. If someone insists on an overpayment, they are trying to rob you. Your skepticism protects your bank account from these deceptive reversal tactics.
Accept only secure payment methods like cash in person or verified digital escrows. These systems protect both the buyer and the seller from the risks of fraudulent checks.
Consult your bank's fraud department if you receive a suspicious check in the mail. They have the instruments to verify the authenticity of the document before you deposit it.
Return the original check to the sender and ask for the correct amount via a different method. Refusing to participate in the "refund" stops the scam before it starts.
7. Secondary Marketplace Shipping Fraud
Fraudulent sellers will provide a tracking number that shows a package was delivered to your city. You wait for the item, but it never arrives at your specific front door. The scammer sent a cheap envelope to a random address in your zip code to generate a "delivered" status. This trick makes it very difficult for you to win a dispute with the marketplace. The system sees a successful delivery and automatically closes your claim for a refund.
Direct communication with the shipping company is required to resolve this issue. You should ask the carrier for the exact weight and the intended delivery address of the tracking number. Compare this data to the item you actually purchased to prove the fraud to the platform. Scammers count on you giving up after the first automated rejection of your refund. Your persistence is the only way to recover your money from a dishonest seller.
Verified sellers with long histories of positive feedback are much safer than new accounts. You should be wary of prices that are significantly lower than the market average for electronics. Use a credit card for all online purchases to take advantage of their superior dispute processes. These financial institutions have more power to reverse a charge than most third - party marketplaces. Your choice of payment method is a fundamental part of your digital security strategy.
Request a photo of the shipping label from the seller before they send the item. Clear documentation of your address on the box reduces the chance of a "wrong house" scam.
Check the weight of the package on the tracking page to see if it matches your item. A laptop should not weigh the same as a single letter or a small postcard.
File a police report if the marketplace refuses to help you with a clear case of fraud. Legal documentation adds weight to your claim and forces the company to take a closer look.

8. Fake Government Grant Notifications
Letters or emails claim that you have been selected for a free government grant for "home improvements." You are told that you never applied but were chosen based on your tax history or location. This message usually includes an official - looking seal and a sense of federal authority. They ask for a processing fee to release the thousands of dollars in your name. The government never gives away money to random individuals through unsolicited emails.
Official agencies communicate through the mail and do not charge fees to collect a legitimate grant. You should visit the official ".gov" website to look for any programs that actually exist. Scammers use these scripts during times of economic hardship to exploit people who need financial help. They will ask for your social security number to "verify" your identity for the grant. This information is used to open new credit lines in your name and ruin your credit score.
Delete any message that claims you won a lottery or a grant that you did not enter. You must be the one to initiate contact with government offices for any financial assistance. Do not click on links in these emails, as they often contain malware that tracks your keystrokes. Protecting your sensitive data is more mandatory than the dream of a free payout. Your awareness of how the government actually functions will keep your money safe.
Call the agency directly using a phone number from their official website. Never use the contact information provided in the suspicious letter or email you received.
Look for spelling errors or informal language in the supposed government document. Federal communications are strictly formatted and rarely contain basic grammatical mistakes.
Tell the sender that you will pick up the check in person at their local office. Watch how quickly they make excuses or stop communicating once you suggest a face-to-face meeting.
9. Employment Recruitment Identity Harvesting
Fake job postings on popular sites look like great opportunities for remote work. You apply and receive an immediate offer without a real interview process. The "employer" asks for your driver's license, social security number, and bank details for "payroll setup." This is a tactic used to harvest your identity for criminal activities. They may also send you a check to buy "office equipment" and ask you to send the change back.
Researching the company on a professional network like LinkedIn is a mandatory step. You should verify that the recruiter actually works for the organization they claim to represent. Legitimate companies do not hire people based solely on a text - based chat or a single email. Be suspicious of any job that pays significantly more than the industry standard for the required tasks. Your time and your identity are too valuable to give away to an anonymous recruiter.
Interviews should happen over video or in person before any personal data is exchanged. You must never pay a company to start a job or buy equipment from their "preferred vendor." Real employers cover the cost of the instruments you need to perform your duties. If a situation feels off, trust your instincts and walk away from the offer. Your professional reputation stays intact when you avoid these predatory employment schemes.
Verify the email domain of the recruiter to ensure it matches the official company site. Scammers often use free email services or slightly altered domains like "https://www.google.com/search?q=company-hr.com."
Search the job description text online to see if it has been used in other scams. Criminals frequently copy and paste the same high-paying job ads across multiple platforms.
Refuse to share your social security number until you have a signed, verified contract. Validating the company's physical address and phone number is a required part of your due diligence.

10. Social Media Account Takeover Tactics
You receive a message from a friend's account asking you to click a link or vote in a contest. This friend has already lost their account to a hacker who is now targeting their contacts. The link leads to a fake login page designed to steal your username and password. Once you enter your details, the attacker takes over your profile to continue the cycle. They may also use your account to promote fraudulent investment schemes to your family.
Directly calling your friend is the best way to see if they actually sent the message. You should never trust an unusual request for money or "help" on a social media platform. These attackers use the trust you have in your friends to bypass your normal caution. They often claim to be in a crisis and need a quick favor to get back into their account. Your digital identity is at risk every time you click an unverified link.
Setting up login alerts will notify you if someone tries to access your account from a new device. You should use a unique password for every social media platform you use. This prevents a single leak from compromising your entire digital presence. Review your active sessions regularly to ensure only your devices are logged in. Your proactive management of your privacy settings is a fundamental defense against takeovers.
Enable a hardware security key for your most sensitive social media accounts. This physical device is the strongest form of protection against remote hacking attempts.
Report the compromised account to the platform so they can freeze it and notify the owner. Helping the platform identify the breach protects the rest of the network from further attacks.
Warn your common friends if you notice one of your contacts is sending out spam. Early notification prevents the virus of misinformation from spreading to more people in your circle.
11. Disguised Charity and Crisis Exploitation
Scammers create fake donation pages immediately after a natural disaster or a major news event. You see emotional photos and stories that pull at your heartstrings to encourage a quick gift. These individuals pocket the money instead of sending it to the people in need. They often use names that sound very similar to well - known international relief organizations. Your generosity is a target for those who have no moral compass.
Checking the registration status of a charity on a site like Charity Navigator is a required step. You should only give to established organizations with a transparent history of how they use their funds. Avoid giving money through social media links or unsolicited text messages. These platforms take a cut of the donation and offer little protection against fraud. Your contribution has the most impact when it goes through official, verified channels.
Request a receipt for your donation to ensure the organization is a registered non - profit. You should be wary of any charity that only accepts cryptocurrency or wire transfers. Real non - profits are happy to accept credit cards because they offer security for the donor. If a caller pressures you to give money over the phone, hang up and do your own research. Your desire to help others should not lead to your own financial exploitation.
Type the charity's name into a search engine followed by the word "scam" or "complaint." Public records and news reports often highlight organizations that fail to deliver on their promises.
Contact your local better business bureau to see if the charity has a history of issues. Official ratings provide a clear view of the administrative costs and the actual impact of the group.
Give directly through the organization's official website instead of a third-party link. This ensures that your money is not being skimmed by a middleman or a fraudulent collector.

12. Hidden Subscription and Zombie Billing
Free trials often require a credit card and bury the cancellation terms in the fine print. You forget to cancel, and the company begins charging you a high monthly fee for a service you don't use. These "zombie" bills can continue for months before you even notice them on your statement. Some companies make the cancellation process intentionally difficult to keep the revenue flowing. Your lack of attention to your bank statements is exactly what these businesses count on.
Reviewing your recurring charges every month is a mandatory habit for financial health. You should use a virtual credit card service that allows you to set spending limits or expiration dates. This prevents a company from charging you more than the agreed amount or continuing a subscription after you quit. Many apps now offer "one - click" cancellations to help you manage these hidden costs. Your awareness of where your money goes is the only way to stop these leaks.
Legal protections exist to help you fight unfair billing practices in many regions. You should contact your bank to dispute any charge that you did not explicitly authorize. Be firm with customer support and demand a confirmation number for your cancellation request. If a company refuses to stop billing you, file a complaint with the consumer protection agency. Your persistence will eventually force the company to stop their predatory billing cycles.
Set a calendar alert for two days before a free trial is set to expire. This gives you enough time to navigate the cancellation process and avoid the first charge.
Read the terms and conditions specifically for the words "auto-renewal" and "cancellation." Knowing the rules of the agreement prevents surprises on your next credit card statement.
Use a dedicated email address for all free trials to keep your main inbox clean. Sorting your subscriptions becomes much easier when they are all located in a single, dedicated place.
Regulatory Verification and Licensing
Legitimacy starts with a check of the official government registers for financial services in your region. Every real platform must hold a license from a recognized authority like the SEC or the FCA. You should search for the license number directly on the regulator's website to confirm it is active and valid. Fake sites often steal the registration numbers of defunct or unrelated businesses to look real to a casual observer. Your capital stays at high risk if the company operates outside of these established legal frameworks.
Financial regulators maintain public databases that are free for everyone to access and search without restriction. You should verify that the company name exactly matches the one listed on the official permit or certificate. Discrepancies in the physical address or the contact phone number are major red flags for a fraudulent operation. Most countries require investment firms to have a physical presence within their borders for legal accountability and service. Your protection under the law disappears if you send money to an unregulated offshore entity that has no physical office.
Rules for investment firms include strict requirements for capital reserves and insurance for client funds to prevent losses. You should look for details about which particular bank holds the platform's operational cash and your deposits. Segregated accounts ensure that your money remains separate from the company's daily business expenses and debt obligations. This structure protects your assets in the event that the platform faces a bankruptcy or a legal seizure of assets. Professional firms are always open about these financial arrangements to build a long - term relationship with their clients.
Search the central database of your national financial regulator for the company's legal name. Official records display a clear history of any disciplinary actions or fines levied against the firm over the years.
Cross - reference the registration number provided on the website with the regulator's list. Discrepancies often indicate a cloned website designed to mimic a legitimate and licensed business to steal your login credentials.
Verify the list of jurisdictions where the company is legally allowed to accept new clients. Financial laws differ by region and an honest firm will be clear about the countries where it legally operates and recruits.
Domain History and Technical Transparency
Criminals frequently set up new websites that look professional but have zero historical footprint on the internet. You should check the registration date of the domain name using a public lookup utility to see its true age. A platform that claims decades of success yet the domain is only three months old is a scam. These temporary sites disappear as soon as they collect enough money from unsuspecting victims to be profitable. Your due diligence must include a look at the technical age of the digital storefront before you commit your cash.
Technical transparency involves a clear disclosure of the software and servers used for trade execution and data management. You should be able to see which liquidity vendors the platform uses to fill your orders in the market. Anonymous setups that hide their technical infrastructure often manipulate price feeds to steal your capital through fake trades. Real platforms use industry - standard protocols that are verifiable by third - party security auditors on a regular basis. Your success depends on a fair and transparent environment for every transaction you make on the network.
Security certificates should be current and issued by a reputable authority for the particular domain name you are visiting. You must look for the "HTTPS" prefix and the lock icon in your browser's address bar to ensure encryption. Fake sites sometimes have certificates that do not match their name or have expired long ago due to neglect. These technical errors show a lack of professional oversight or a rushed attempt at fraud by the developers. Your data remains vulnerable on any site that fails to maintain these basic technical standards for its users.
Perform a WHOIS search to find the original creation date of the platform's website. Scammers often buy old domains to fake their history, so check for recent changes in ownership as well to be sure.
Inspect the source code of the login page for any suspicious third - party tracking scripts. Malicious code is able to harvest your credentials before you even finish the login process on a fake site or app.
Check the physical location of the servers using an IP geolocation lookup utility. Discrepancies between the claimed headquarters and the server location should prompt further investigation into the company's true origin and location.
Financial Transparency and Withdrawal Protocols
Clear rules for how you get your money back are the mark of a legitimate business in any industry. You should read the terms and conditions for any mention of "withdrawal fees" or "minimum balances" before you deposit. Scammers often hide these details to trap your funds inside their system indefinitely while they charge you fake fees. A platform that makes it hard to leave is likely trying to steal your entire investment through complex rules. Your ability to liquidate your position at any time is a fundamental requirement for the safety of your funds.
Fee structures should be simple and easy to calculate before you make a single trade or investment. You should avoid any service that charges "release fees" or "taxes" that must be paid upfront before a withdrawal. Legitimate firms deduct their commissions from your existing balance or your profits automatically as part of the service. These extra demands for cash are a classic sign of an exit scam designed to bleed you dry of your remaining money. Your logic tells you that a business should never ask for more money to give you back what you already own.
Audit reports from independent third parties confirm that the platform actually holds the assets it claims to manage. You should look for a "Proof of Reserves" or a similar document on the company's website for verification. These audits confirm that the numbers on your screen match the physical or digital assets held in the vault. Transparency in the back end is the only way to ensure the firm is not a Ponzi scheme. Your wealth is only real if the platform is able to prove it exists in a secure and verifiable way.
Test the withdrawal process with a small amount of money before you deposit a large sum. Reliable platforms process these requests within a few business days without any unexpected hurdles or delays for the user.
Read the fine print for any clauses that allow the company to freeze your account without cause. Unfair terms give the platform legal cover to steal your assets under the guise of security checks or compliance reviews.
Compare the listed fees with the industry average to spot any hidden or excessive charges. Drastic differences in cost often hide a predatory business model that profits from your confusion rather than your success in the market.
Security Features and Data Protection
Multi - factor authentication is a requirement for any platform that handles your personal wealth in the digital age. You should look for options that include hardware keys or app - based codes rather than just SMS messages. Text messages are vulnerable to SIM - swap attacks that are able to bypass your security in seconds without your knowledge. A platform that takes security seriously will force you to use the strongest methods available to protect your account. Your account is only as secure as the weakest link in the authentication process you choose to use.
Data encryption protocols protect your sensitive information as it travels across the public internet to the servers. You should confirm that the site uses advanced standards like AES - 256 for all stored data and transactions. Real firms are open about their encryption methods and their data retention policies to build trust with you. They should also have a clear plan for what happens in the event of a data breach or a hack. Your identity is a valuable target for thieves, so you must ensure it is under lock and key at all times.
Internal security controls prevent unauthorized employees from accessing your private financial data without a valid reason. You should ask about the company's policy on background checks and internal access logs for their staff. Large firms use a "zero trust" architecture to minimize the risk of an insider threat to your account. These measures ensure that only the most necessary personnel is able to see your account details for service purposes. Your peace of mind comes from knowing that the platform prioritizes safety at every level of its internal operation.
Enable login notifications to receive an email or text every time your account is accessed. Immediate alerts allow you to take action if a hacker gains entry to your profile from an unknown device or location.
Check the site's privacy policy to see if they sell your data to third - party marketing firms. Honest businesses protect your information rather than treating it as a product to be sold to the highest bidder for profit.
Review the platform's history for any previous data breaches or security failures. Past performance in security is a good indicator of how well the company will protect your assets in the future under stress.
Reputation and User Feedback Analysis
Public opinion on forums and review sites displays an unfiltered look at the user experience on the platform. You should look for patterns in the complaints rather than just single instances of bad luck from a user. If dozens of people mention that withdrawals are impossible, the platform is almost certainly a scam designed to steal. Genuine reviews contain exact details about the interface, the support, and the speed of the service you should expect. Your research should include sources like Trustpilot, Reddit, and specialized financial forums that track industry trends and frauds.
Social media presence reveals a lot about how a company treats its customers in public spaces and during crises. You should check the comments on their official posts to see if people are complaining about missing funds or poor service. Scammers often turn off comments or delete negative feedback to maintain a clean image for new victims. A lack of transparency in public interaction is a sign that the firm has something to hide from the world. Your trust should be reserved for companies that handle criticism with professional and helpful responses to their users.
Historical news coverage tells you if the founders have been involved in previous fraudulent schemes or legal issues. You should search for the names of the executive team to see their professional background and their reputation. Many serial scammers move from one failed platform to the next with a slightly different brand name and logo. A team with no history or a track record of failed businesses is a massive risk to your capital. Your decision to invest should be based on the integrity and experience of the people in charge of the company.
Search for the platform name on social media to see real - time discussions among current users. Unfiltered conversations often reveal technical glitches or withdrawal issues long before they hit the official news cycle or reports.
Look for professional reviews from reputable financial journalists and industry experts. Independent analysis results in a level of depth that regular user reviews lack due to emotional bias or lack of knowledge.
Verify the company's address on a map to see if it belongs to a real office building or a virtual mailbox.Scammers often use the addresses of famous skyscrapers to look more prestigious than they actually are in the real world.
Mobile Application Integrity and Permissions
Mobile apps are often the primary way users interact with their investments and monitor their accounts today. You should check the permissions the app requests upon installation on your device to ensure they are reasonable. A trading app has no reason to access your contacts or your private photo gallery to function properly. These overreaching requests are a sign that the software is designed to harvest your personal data for profit. Your privacy depends on your willingness to deny unnecessary access to your hardware and your information.
Official app stores like Google Play or the Apple App Store have basic security screenings for every listing they host. You should read the developer information to see if it matches the official company website and its branding. Fraudulent apps often use a slightly different name to trick people into downloading them for a fake service. The number of downloads and the variety of reviews is also able to give you a clue about the app's legitimacy. Your account security is at risk if you install a malicious app from an unverified third - party source.
Updates for the application should be regular and address known security vulnerabilities or bugs in the code. You should look for a clear changelog that explains what each new version accomplishes for the user experience. A developer who abandons their software leaves your data open to exploitation by hackers who find old flaws. Real companies invest heavily in the maintenance of their mobile platforms to protect their users and their brand. Your device remains a safe gateway to the markets when the software is kept up to date by the team.
Inspect the privacy labels in the app store to see how the developer handles your data. Clear disclosures about data collection are a requirement for all legitimate financial applications in the modern market.
Read the reviews specifically for complaints about app crashes during withdrawal attempts. Technical failures at critical moments are often a deliberate tactic used by fraudulent platforms to prevent you from leaving.
Verify that the app uses biometric login features like fingerprint or facial recognition. These advanced security measures add an extra layer of protection to your financial assets while you are on the go.
Customer Support Accessibility and Quality
Live support should be available through multiple channels like phone, email, and chat for your convenience. You should test the response time by asking a technical question before you fund your account with real money. A legitimate firm will have a professional team ready to assist you with any issues or questions you have. Scammers often rely on automated bots or simply ignore messages once they have your money in their possession. Your peace of mind relies on knowing that help is available when you need it during a market event.
Knowledgeable staff members are a sign of a company that invests in its human resources and its clients. You should pay attention to the quality of the answers you receive from the support team during your test. If the agent gives vague or evasive responses, you should view this as a major red flag for the company. Real professionals are able to explain complex financial concepts in a way that is clear and direct for the user. Your financial safety is tied to the competence of the people who manage the platform and its services.
Emergency contact information must be easy to find in case your account is compromised or you see a hack. You should look for a dedicated security hotline or an urgent support email address on the main page. A platform that hides its contact details is trying to avoid accountability for its actions and its failures. You should be able to reach a human being who can freeze your account in seconds if it becomes necessary. Your control over your assets depends on the speed and efficiency of the support team when things go wrong.
Check the physical address of the support office to see if it is a real location. Verified businesses are open about where their customer service teams are based to provide a sense of security.
Ask the support team about their process for resolving disputed transactions. A clear and fair policy shows that the company values its reputation and its customers over short - term profits.
Review the availability of support during the hours when the markets are actually open. Financial services should be reachable during the times when you are most likely to be trading or moving your funds.
Educational Content and Marketing Ethics
Ethical marketing avoids the use of high - pressure tactics and unrealistic promises of wealth to attract new users. You should be wary of any platform that uses "FOMO" to drive new signups among its target groups. Honest firms explain the risks of investing just as clearly as they explain the potential rewards for your portfolio. They do not use flashy advertisements that make the markets look like a casino or a game. Your long - term success depends on a realistic and grounded view of the financial world and its risks.
Quality educational resources show that a company wants its users to succeed over the long term in the markets. You should look for webinars, articles, and tutorials that cover the fundamentals of risk management and analysis. A platform that only pushes you to trade more is looking out for its commissions rather than your account balance. Genuine education helps you make better decisions and protects you from common market pitfalls and emotional mistakes. Your growth as an investor is supported by a firm that prioritizes your knowledge and your skill development.
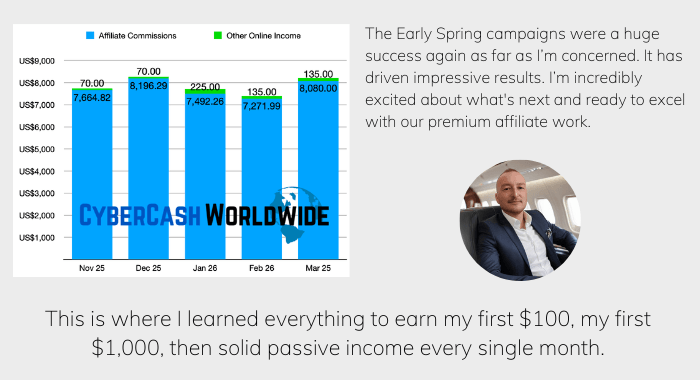
Transparency in advertising includes a clear disclosure of all partnerships and affiliate relationships used to grow the site. You should know if the person recommending the platform is being paid to do so by the company. Scammers often hire influencers to promote their fraudulent sites to a wide and trusting audience for a quick profit. A legitimate company will have a clear and ethical affiliate policy that follows advertising laws and standards. Your trust should be earned through honest performance rather than paid endorsements from people who do not use the service.
Look for a clear risk disclaimer at the bottom of every page on the platform. Financial authorities require these warnings to ensure that investors are aware of the potential for loss in every trade.
Evaluate the tone of the company's social media posts for any signs of predatory marketing. Professional firms maintain a sober and analytical voice rather than promising guaranteed riches to their followers or their clients.
Analyze the quality of the free training materials provided to new account holders. High - value education is a sign of a company that is invested in the long - term health of its client base and its reputation.
Examples Of Common Online Scams Like Rotten Chili Dogs: Conclusion
The digital world requires a level of vigilance that goes beyond simple common sense. You have analyzed twelve distinct ways that scammers attempt to separate you from your money and identity. Each of these traps relies on a combination of technical deception and emotional manipulation to succeed.
Your defense depends on your willingness to slow down and verify the facts before you take action. Modern criminals are persistent, but they are also predictable in their use of high - pressure scripts. You must prioritize your security settings and maintain a healthy level of skepticism toward all digital communication.
Protecting your assets is a continuous process that requires both technical instruments and mental discipline. You are now better prepared to spot the warning signs of a "rotten" deal before it ruins your financial health. Keep these lessons in mind as you move through the internet every day.




please help how can i get money back, I called u but it was no answer. please sir.